11 Sep 2020
Show Me Your Anchor
Proverbs 29:18 contains one of the more widely quoted verses from the Bible.
“Where there is no vision, the people perish: but he that keepeth the law, happy is he.” (KJV)
I recently read the Christian Standard Bible’s translation, which is slightly different.
“Without revelation* people run wild, but one who follows divine instruction will be happy.”
The choice of the term revelation in the CSB translation appeals to me. The authors included a footnote for their choice of revelation, saying it can also be read as vision. The more I have learned about Jesus and our heavenly father, the more I have learned that we really only “discover” things on earth, even when we invent. The Latin root of the word discover is discooperire, “uncover,” which combines the prefix dis-, or “opposite of,” with cooperire, “to cover up.” So discover really means to remove the cover on something which was always there. That’s what revelation and vision are: the time has arrived to remove the cover.
The phrase “people run wild” adds amplification to “perish” in the original KJV version. Perishing itself is a process, and manifests after an extended period of running wild. I was once told by a pastor that the best way to understand Proverbs 29:18a is “Without vision the people cast off all restraint”. This is better way of understanding running wild. It’s interesting to think of that interpretation in the context of what has been going on in the past two decades , and is now moving into the next logical phase in this year of 2020.
So with the insights of the old and new translations, and the context of this year 2020 (which so many are anxiously awaiting its end), it is easy to see the progression which has been going on for a long time, and culminating in what we are starting to see today.
- Push God to the side, as less important than something else.
- When the consideration of God and being accountable to Him is not number one in your life, there is nothing stop you from doing something which you know He would not approve of.
- When you have done something which you know doesn’t please him, push God further away so that He is not bothering you anymore.
- When there is finally no influence from God (which can accompany total forgetfulness of God or unthrottled hostility), there is no ultimate accountability.
- When there is no ultimate accountability, there is no reason I should not do anything I want. (this is known as relative morality)
- When I can do anything I want, there is no reason anyone else should not be able to do what they want.
- When everyone realizes that they can do what they want, trust erodes and fights break out over what little there is. (God has halted his blessing of abundance by this point).
- Finally, the point of perishing sets in.
Perishing is when God has removed his blessing and allows judgement. And it is not what most people expect. Most people expect things to fall from the sky, nasty storms, maybe even lightning blasting people from the sky like a laser, or a series of bad luck which can’t be explained.
His judgment is actually more straight-forward: it’s subtle yet observable. He simply gives everyone more of what they are doing, and does not hold back the consequences. The consequences won’t be felt at first: God’s enemy has no interest in making a person’s life miserable, until they have fallen far enough into his trap. Remember, the devil is not a creature with a pitchfork and a pointed tail, and doesn’t look threatening. That would work against his cause. He will always appear as a beautiful, self-confident creature, and the thing you have chosen will be sold to you as great, not harmful. The Bible even says the devil was the most beautiful creature in heaven–before the fall. He can even masquerade as an angel of light, and fool those not close to God.
If the person does not repent and cry out to the Lord, they are drawn into an endless cycle of desensitization and needing more of their sin or idol to maintain the pleasure expected from it. It doesn’t matter what it is: money, sex, power, drugs, alcohol (and includes even politics and political figures). He won’t stop whispering to us our about need to let go and come back, but he also will not hold back on the growing negative consequences if we chose to cling to our addictions and idols. And the devil will always be pulling the guilt strings to try and stop us from responding to the Lord. “How could God love or forgive you after what you did?” But that’s exactly what He does. (Doctor) Jesus pointed out that it is not the healthy who need a doctor.
Ultimately everyone needs to realize when they are in this cycle, and to get out… immediately! “Everyone who calls on the name of the Lord will be saved.” (Romans 10:13). The running wild part of life is not hard to recognize. You just have to slow yourself down enough to see it. So abandon your addictions or idols, and run back to the restraint which comes from loving the Lord. The only thing that is hard to know is when the point of perishing will arrive. And that’s a game of chicken or a dare that no one should ever accept.
Get out with Jesus, while you still can. His love never fails and his forgiveness is available for the asking, but you have to be in it … before the grace period is over.
10 Aug 2020
Asking For Forgiveness… An Earthly Example of How Not To Do It
In 1833, the Supreme Court took on one its more unusual cases: UNITED STATES v. GEORGE WILSON
The case does not appear that special at first glance. It involved two defendants named James Porter and George Wilson. They were accused of a few instances of obstructing the United States mail service, and assaulting and wounding a mail carrier in 1830. They were both convicted and sentenced to death.
James Porter was put to death on July 2nd, 1830. But George Wilson was different. Prior to the judge pronouncing their sentence on the morning of May 27th, 1830, George Wilson recanted his not guilty plea in court and changed it to a guilty plea. It did not change his sentence.
On June 10th, with George Wilson’s friends pleaded with President Andrew Jackson for his life, and the president issued a pardon for the crime which caused him to receive the death penalty. Later in October, George Wilson rejected the pardon in a reconvened court by saying nothing.
WHAT???
The President of the United States of America takes the time and effort to issue a reprieve, and it is not used? What’s going on here?
This case was so unusual it was heard by the United States Supreme Court. Evidently this was new ground for a convict to reject forgiveness.
The Court ultimately ruled, and this is a quote from the detailed document at Cornell’s web site below:
This court is of opinion, that the pardon in the proceedings mentioned, not having been brought judicially before the court, by plea, motion or otherwise, cannot be noticed by the judges.
To use an analogy, it’s like playing the game monopoly and drawing a “Get Out of Jail Free” card. If you don’t take the initiative to play the card when you land on the dreaded Go To Jail spot, the card is useless–even if you just forget to play it before the next person’s turn.
George Wilson was hanged in the end, despite a pardon on the table for him just for the asking.
George Wilson had done nothing to earn a pardon. President Jackson was responding to a group of petitioners who approached the president on George Wilson’s behalf. Prayer groups do the same on behalf of their friends, family, and many others they do not even know. They petition Jesus to draw them to salvation. They are not asking Jesus to actually forgive them: he has done that already. They (we) are asking Jesus to intervene and bring the person to the awareness of it, the acknowledgement of it, and ultimately the desire to cry out to Him for it.
Our prayer is to remove the person’s obstacles to accepting Jesus’ salvation. “For everyone who calls on the name of the Lord will be saved.” — Romans 10:13 (CSB)
Jesus is not our errand runner, nor is He some kind of puppet master. He is a loving Father, and the King of Kings. The Supreme Court said in their ruling, when the petitioner pleads, only then will the court hear it. Jesus does likewise: he offers the forgiveness (pardon) which is already complete, but he will not force it on anyone.
This decision by the Supreme Court has so much Godly wisdom in it. George Wilson’s admission of guilt didn’t change his sentence. God’s word tells us that all have sinned and fallen short of the glory of God. Simply admitting that we have sinned is a good step, but by itself it won’t undo the sentence of eternal death. We have to cry out to Jesus for his pardon of our sins. He’s already created it and signed it, but we have to add our signature to it. Otherwise, we will hear the dreaded words at the great day of judgement: “Depart from me you sinners, for I never knew you.”
Also, what motivated George Wilson to ignore the pardon will always be a mystery. But I can give a multitude of speculations why, which would even apply today to those who have not accepted Christ.
- Did he have a misguided loyalty to his partner in crime? He confessed but his partner James Porter had not. Did he feel it was not fair unless James was pardoned as well, and he would die for that opinionated sense of fairness? After all, he may have seen good sides of James having spent so much time with him. A person who is fully evil is indeed rare. Why save me and not him?
- Did he have a masochistic personality or conscience? Did he feel that he was not worth the attention of the President, or embarrassed to admit that what he had done was so bad that he needed a pardon? In fact, why wouldn’t someone admit that the president must see something worthy of a pardon? Presidents do not issue pardons like candy. Neither does Jesus.
- Was there a bad incident or imprint with the government in his past which caused a level of hate or distrust strong enough to push this away? It is common to hear people discuss something about pain or hurt by a church’s members from people who have walked away from God. Despite whatever hate or distrust exists, a pardon is still a pardon. It’s authority does not change. Leaders in higher positions always look at things differently (more broadly) than lower level leaders do.
This list could on and on. The sole question which George Wilson had to answer is the same one we have to answer with Jesus: what or who are we letting stand between the King who sees things differently than us, and extends his offer of pardon directly to us–bypassing any and all middlemen.
Don’t wait to accept the invitation: George Smith missed his chance to have things made right. And unlike George, we have the problem of not knowing when our death will occur.
Too many people wait for the 11th hour to do something critically important, only to die at 10:30. Cry out to him now for that pardon. Time is short.
Wikpedia summary of the case: https://en.wikipedia.org/wiki/United_States_v._Wilson
Full document at Cornell University’s web site: https://www.law.cornell.edu/supremecourt/text/32/150
Note: Be prepared for wordy, run-on sentences in the 19th century text of the full document.
01 Aug 2020
Seeing The Works of God Through His Eyes
Ezra 3:10-13 (CSB)
When the builders laid the foundation of the temple of the Lord, the priests in their vestments were stationed to praise the Lord with trumpets, and the Levites, the sons of Asaph, with cymbals, according to the directions of King David of Israel; and they sang responsively, praising and giving thanks to the Lord,
“For he is good, for his steadfast love endures forever toward Israel.”
And all the people responded with a great shout when they praised the Lord, because the foundation of the house of the Lord was laid.
But many of the priests and Levites and heads of families, old people who had seen the first house on its foundations, wept with a loud voice when they saw this house, though many shouted aloud for joy, so that the people could not distinguish the sound of the joyful shout from the sound of the people’s weeping, for the people shouted so loudly that the sound was heard far away.”
Recently I found myself falling into a classic mental trap: bitterness. And the Lord rebuked me for it. He used the verses above to show me the source of the problem.
These verses document the reactions of two generations of Israelites to the wonderful start of God’s magnificent work rebuilding the temple. The newer generation is very enthusiastic, shouting with joy. The older generation is weeping loudly. That generation had seen the first house on its foundations, and its destruction. It left an imprint of hurt on them.
And that imprint was so strong, that a truly magnificent work of God was souring their minds instead of causing them to rejoice. After all, God is the redeemer. He was rebuilding something the enemies of God had destroyed.
God is moving in a big way in America and the world: this bizarre year of 2020 has caused everyone to rethink so many things in their lives, myself included. I love Jesus, and pray that He move in America and restore it. YET, there was one thing which began to creep into my prayers. To paraphrase it, I was asking him, “Restore America, but if the people just want you to restore things the way they were… I won’t ask you to delay or retreat from its judgment.”
When you’ve lived a long time, it’s important to fight a tendency to think that your greater experience (than what you had in your youth) allows better insight into what we ask God. It creates a false of sense of security and confidence in us, and honestly–a cheap excuse to allow for a door of failure. That is the wrong way to think.
There’s an important concept in these verses not to miss. Despite rebellion and unbelief which led to the events which caused the first temple to be destroyed, God chose to forgive the Israelites and set things in motion for a successful rebuilding of a temple. How could any children of God mourn that?
He can do that with America. Notice carefully, that this event in Ezra isn’t at the completion but at the start of building the temple. How much different would the celebrations be at the completion. So we are now with God’s work at this point in history. He has work which will soon produce a massive harvest, but … it is still in progress.
The Lord was reminding me not to judge (which no Christian is supposed to do), and pray to God for the desire of the heart… with no concern of how He will do it. His works are to be celebrated, not judged by our vision or standard we have formed, nor tainted by the past… which is over. This must also be reflected in our prayers.
Mathew Henry wrote a commentary on this verse over 300 years ago, which says it in a very elegant way.
There was a remarkable mixture of affections upon laying the foundation of the temple. Those that only knew the misery of having no temple at all, praised the Lord with shouts of joy. To them, even this foundation seemed great. We ought to be thankful for the beginnings of mercy, though it be not yet perfect. But those who remembered the glory of the first temple, and considered how far inferior this was likely to be, wept with a loud voice. There was reason for it, and if they bewailed the sin that was the cause of this melancholy change, they did well.
Yet it was wrong to cast a damp upon the common joys. They despised the day of small things, and were unthankful for the good they enjoyed.
Let not the remembrance of former afflictions drown the sense of present mercies.
17 Jun 2020
From Slippery Slope to Avalance.. an Old Warning for a Modern Time (Genesis 6:1-6)
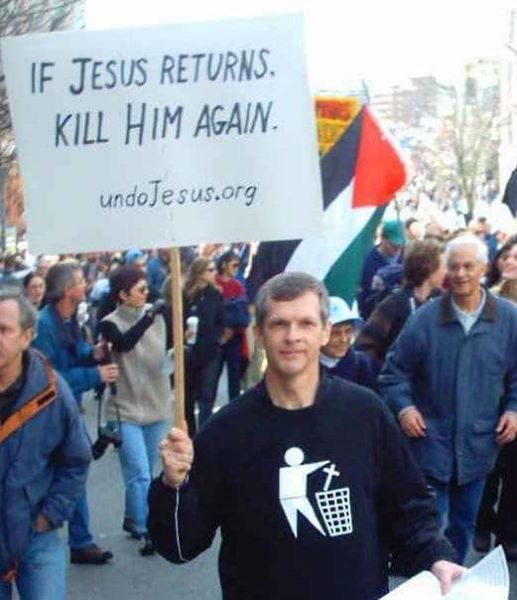
This picture was taken at a 2004 in a protest in Vancouver Canada against the Iraq war, and is truly heartbreaking. We have slowly watched the God of Israel being pushed out of Western culture over the decades, and other counterfeits taught in His place. So events like this are becoming more commonplace–and bolder as time progresses.
And what does this protester hope to achieve? At a minimum he is in front of a camera , so a need of recognition is there–whether for a cause or himself, or both. This picture is the best demonstration of a hurting heart masquerading as a hard heart, but hopefully not of a seared-conscious. We have far too much of that in the world as it is.
Don’t give up hope on him, or condemn him even if just in your mind. As loud as the sign is and as offensive as it appears (which it is what it is designed to do), God’s not rattled by it. Neither should you be. God just smiles, because this is exactly the type of person he chases in love to expose the enemy’s lies and His truth. This man is at a protest today, but where will he be in 3 months, 6 months, maybe even a year. Will he be married, and have a child (which suddenly changes EVERYONE’s mind about the existence of God if they have any love in them at all).
I know, because in some ways I was like him. Will his actions (like all of our actions) become artifacts which the Lord later uses for his glorification. This is a true statement: our actions ultimately testify to God’s work in one of two ways. They demonstrate things that align with the Lord, or they don’t. It’s our call.
To understand what you are seeing happening around you in these frantic times, it is very important to understand what led up to this. There are some very good parallels in Genesis 6:1-6. You know, it’s in that Myth of the Bible. The one which so many people have been taught to refer to this way, despite the fact of its longevity and it being the entire basis of the Western society we live in. Chapter 6 begins to describe the events leading to the great flood: the first judgement against mankind which God had to do.
One of my favorite commentators on the Bible is Matthew Henry (our pastor jokingly refers to him as the church’s associate pastor). Matthew Henry wrote his commentaries not long after the publication of the King James Bible (which appeared thanks to the invention of the printing press). Considering when they were written, the profound insight endures to this day as one of the best commentaries ever written. I encourage you to read Genesis chapter 6 for the actual text, but here is Matthew Henry’s commentary on the first few verses (emphasis with bold text is mine):
For the glory of God’s justice, and for warning to a wicked world, before the history of the ruin of the old world, we have a full account of its degeneracy, its apostasy from God and rebellion against him.
The destroying of it was an act, not of an absolute sovereignty, but of necessary justice, for the maintaining of the honor of God’s government.
Now here we have an account of two things which occasioned the wickedness of the old world:-1. The increase of mankind: Men began to multiply upon the face of the earth. This was the effect of the blessing (ch. 1:28), and yet man’s corruption so abused and perverted this blessing that it was turned into a curse. Thus sin takes occasion by the mercies of God to be the more exceedingly sinful.
Prov. 29:16, When the wicked are multiplied, transgression increaseth. The more sinners the more sin; and the multitude of offenders emboldens men. Infectious diseases are most destructive in populous cities; and sin is a spreading leprosy. Thus in the New-Testament church, when the number of the disciples was multiplied, there arose a murmuring (Acts 6:1), and we read of a nation that was multiplied, not to the increase of their joy, Isa. 9:3. Numerous families need to be well-governed, lest they become wicked families.
“The multitude of offenders emboldens men.” Notice that it does not say justifies them. Our culture has been taken over by entertainment, comfort, pop-culture and many things which encourage people to seek the experience and cruise on their emotion-of-the-moment. There are people who will go to BLM protests (or any other public gathering) and take loads of selfies and share them with the world to surf the emotion of being there. And emotions are something God’s enemy really knows how to manipulate.
The real problem, as Matthew Henry points out, is that it is easy for sin and wickedness to grow in the absence or sparsity of God’s influence. Persecution (and shaming is part of that) comes from the attitude of “we all think this way, why shouldn’t you?” It’s when mob mentality takes over: one of the things most likely to occur when a group of disgruntled people get together thinking they have the same pure motive. As a longtime friend of mine recently pointed out, a mob is the devil’s playground. It leads to the violence and destruction we see, when the emotions–already elevated–are easily pushed over the edge. The more a person is angry, the more rational thinking is shutdown.
——————
So keep people who think like this protester in your prayers to God. You see, we’ve been warning about slippery slopes for years. But when the avalanche comes, the people holding up signs like this will suddenly come to the realization that they were wrong and are in trouble. And even people flaunting signs like this will change. It has happened over and over throughout history.
They will need help and guidance, and the Lord will be sending them to us to help provide that. Just like he sent other believers to us, in the last moments of our previous lives in darkness–when we were disillusioned and had lost hope.
It will be big, so prepare now.. especially your heart.
NOTE: The original post described the picture as being from a recent protest with Black Lives Matter, but it was from a much earlier time… and I have corrected that description above.
12 Jun 2020
Spare Computing During a Crisis.. Helping to Fight the Crisis
I recently discovered a distributed computing project for COVID-19 DNA research called Rosetta@Home ( https://foldforcovid.io/ ). Having 8 Raspberry Pis which are lying dormant after I completed a project with them, I decided to put them online as workers.
For security precautions, I decided to create a segmented guest network on my router for the Pis to operate on: a standard precaution I use. The software for the Raspberry Pi’s is well-written, and even provides a status web page on the localhost to monitor its progress, and even whether it is active.
There are some places which have enormous computing power available, serving no purpose during the COVID related shutdowns: the Miami planetarium is a prime example. They have donated their server’s CPU time to the project until they re-open.
The University of Washington posted some interesting cost comparisons for this project. The cost of distributing the work to the community of spare computers on the internet is about $122,000 versus hosting on Amazon AWS at $175 million.
Having worked in the open software community, which I love, I am really happy to see the influence the open computing can have on a project like this. If you’ve got a raspberry pi (or a unused laptop or desktop computer) laying around, check the site out on how to contribute to the project.
02 Jun 2020
Government… Indirect to You!
You may have noticed a wave of channels removed recently by Google for violating content policies, and the screams from their owners about foul play–even outright censorship. There are very important constitutional concerns about arbitrary removal of content. And viewed at its face value, it seems like targeted censorship.
And then today, there is the Facebook virtual protest over Mark Zuckerberg’s decision not to label or remove President Trump’s tweets as violence inciting. And at a time when the President is preparing to release an executive order to regulate social media activity.
But what’s really going on… and all of a sudden?
There are some proposed changes in bills being worked through Congress, which are a big catalyst for this. The primary one is a change to the protections which internet media distributors have had for a number of years now. This includes social platforms, especially. Essentially, the current law provides legal protection to the distributor of material, as long as it was not the provider. That means that if a social media account is used to post an article, commentary, instructions, etc… the company providing the social media account can not be held liable for that content because it is only a posting location (repository, if you will). Only the content provider (or source of authorship) is liable. In the real world, it is similar to suing a library for the choice of books it has in its selection. The law would protect the library, but not the publisher/author who are responsible for the content.
So Alex Jones (of Infowars) and others have always been liable for their controversial content. There is no change there. But the protections for the social media companies from liability are now at risk to be watered down or virtually eliminated. The threat from this change in the law is forcing social media platforms off of their neutral stance, and causing them to remove content from owners which put them at risk of being sued. And it is very wise for a business to take these precautions, even when it is not law and only looks like the legislation will pass. There’s targeted censorship here, but for motives other than what people attribute it to.
And as far as Trump’s tweets are concerned, I actually empathize with Mark Zuckerberg… something I don’t do often. He (certainly with support from a knowledgeable staff) made the decision to not label them and not to censor them. Not an easy call with all the peer pressure behind that. By contrast, Twitter has chosen to be quite aggressive with banning content, removing posts and labeling content. But is that the right path? Twitter has (rightfully) drawn heavy criticism for doing that.
Twitter and Facebook have taken a passive stance as well on posts, labeling them as containing certain types of dangerous content. I am neutral on this, except when it comes to political figures. I am fine with a song being labeled as having potentially dangerous lyrics, just as I am fine with a health warning on food items and especially on dangerous items like tobacco. It is not stopping me, but it is communicating a danger.
But applying these same warning idioms to political figures and their speech crosses the line between objective and subjective. And subjective includes opinions, something which must be especially protected in the political arena. It is the core of free speech protection.
Finally, there is also a political side of this which may not be immediately apparent. Trump’s tweets are provocative, and have been even since he was campaigning. Obama tweeted in a more traditional way, as a press release. One of the things which I chuckle at (in a macabre way, I admit) is how Trump gets people mad who are dedicated trolls or just loud advocates on social media, because he is just as good on social media with stirring things up as they are. And they are clearly aggravated by it. For social media participants, it’s a rough way to get a wake up call on the real effects of receivers when just spouting out your thoughts. But that is how it should be seen: a wake up call.
Part of a consideration in Facebook’s decision also has to be a concern about creating a dangerous Catch-22 situation. On one hand, the legal protection of them as a distributor is at risk. But if the President signs an executive order prohibiting alteration, removal or appending to original material, then the threat of lawsuits from that proposed law change gets far worse. Social media would be sued by people who they are taking offline, as well as others for not taking people offline. A really, really bad situation for social media companies.
The whole thing just highlights the real problem with social media. It doesn’t really show who we are, it just amplifies what we want to see.
A pastor this past year gave a message celebrating mothers on Mother’s Day, which demonstrates what I mean. In his message, he mentioned the list of traditional things a mother does for the family… and reminded everyone not to forget the newest important role mom’s play in the family: Family Social Media Marketer.
07 Apr 2020
“Pay No Attention To That Man Behind The Curtain”
That’s the famous line from the Wizard of Oz. The Wizard is putting on quite a show for Dorothy, The Tin Man, The Scarecrow and The Lion, filled with smoke, lights, a large and scary projected picture of himself on the wall, while he is sternly shouting loud and bullying threats over a loudspeaker. They get really scared and the masquerade continues, unrecognized, until …
A little innocent dog grabs the curtain in its teeth and pulls it back… revealing the simple old man working a set of levers and controls to put on the show which was mesmerizing… but it was all a show.
And this can be said about the COVID-19 pandemic as well. Don’t make the mistake of reading this as COVID-19 is fake. It is very real, and is more dangerous than a standard flu. But our perception of reality is so influenced by our source of information, we can not forget the need to step back and ask ourselves what have we been looking at. AND DISINFORMATION IS A WAR TACTIC, so evaluating everything with a highly critical eye is important–especially looking for things not being shown.
Also remember that the term “false flag” does not mean fake. It means that whatever flag is being waived (real or generated), it is being used to distract attention from something else.
This virus is a bio-hazard level 2. The media has been showing people wearing level 3 and even Level 4 (Ebola-level) protection.
Vladimir Putin visiting a laboratory in Russia supposedly with Corona virus (from Rossiya 1), and Chinese police in an airport.
The Corona virus is nothing new. It is simply a strain of virus which is normally found only in animals, but sometimes appears in humans. Bird Flu, SARS and MERS are also from the same strain. But look at what the media chooses to put in front of people. Vladimir Putin (pictured during a visit to a laboratory above) is visiting in a level 3 protective suit. Did you notice the others with him simply have standard masks, not a sealed suit with filters as Putin is wearing? You could argue that Putin is being given extra precaution being a national leader, but I also find the yellow suit and red sign more likely placed there to grab people’s attention. For those of you not in the marketing world, red and yellow are the two colors used for grabbing your attention.
This type of media-driven exposure is playing out everywhere, and worse… it is louder than ever before because of social media. I have long pointed-out that one of the most poisonous things I have seen in news reporting (apart from the line between information and entertainment being ever more blurred), is that even reputable newspapers and television news have stooped to allowing National Enquire-like click-bait on the margins of their web pages to finance their operation. Those emotion triggering headlines make money, and with a hyped up situation like this, why wouldn’t they participate in the same type of rib-poking journalism as their click-bait ads do. It obviously generates income.
The news media has traditionally only reported the facts, then shut up and let people evaluate and form their own opinions. Nowadays, countless talking heads are interviewed to sway a person to an opinion–and not let the viewers form their own. A perfect scenario for creating propaganda.
It is not called TV Programming by accident.
Ironically, at the peak of the virus epidemic in China, President Xi Jinping just wore a simple RM1 facemask to visit those effected areas. That’s part of level 2 protection, and a common practice in Asia when the other strong flus (like SARS and MERS) broke out in that area.
The virus is constantly compared to itself. No side-by-side numbers are compared against another virus outbreak.
Forerunner Church in Kansas City, Missouri, recently hosted a Q&A on the virus with Dr. Kenneth Lim, Harvard University Fellow (Forerunner Church COVID-19 Panel Discussion). There is a section of that discussion (from 52:45 to 1:11:04) where Dr Kim elaborates on the following:
- How it impacts the body compared to a normal flu, and how it spreads.
- Survivability of the COVID-19 virus in various environments.
- The lessons learned by Hong Kong, Taiwan and Singapore from Bird Flu (SARS).
- The lessons learned in Philadelphia and St Louis during the 1918 Influenza (the origin of the social distancing strategy).
COVID-19 is dangerous and has a higher mortality rate than a normal flu, but don’t make the mistake of thinking that’s lots of people don’t already die every year from a flu virus. As of Saturday, March 28, there have been 30,300 deaths caused by COVID-19 worldwide. But during the 2018-2019 flu season, the CDC estimates that 61,099 people died from the various flu outbreaks. Wow, that’s a lot…. and that number is just the flu cases in the United States (CDC 2017-2018 Flu numbers). The worldwide fatalities were in the range of 290,000 to 650,000 (NIH site: “Global mortality associated with seasonal influenza epidemics” by the University of Edinburgh).
This is not any attempt to desensitize the value of life or downplay COVID-19, but to give some perspective. Today, everyone puts everything on a graph–which is good to visualize data. But a graph causes a loss of perspective if it not compared with the same graph of something else similar in nature. John’s Hopkins University (and some others) have made very good graphs that would make someone in a War Room of the 1950’s jealous, because the information on those graphs is so much richer and more up-to-date. But taken at face value without context or comparison, it is easy to become mesmerized. Something similar happened with the 24-hour coverage of Operation Desert Storm back in early 1991. People were getting so wrapped up in it, many forgot to shut off the TV and go live their lives.
The constant focus on the media’s portrayal of the virus (and it is intentionally hyped, make no mistake about that) induces internal panic and disruption. And that is a recipe for abuse. This is also the purpose of DISINFORMATION: it is to draw attention away from things which are supposed to be “under the radar”, and are thereby missed by the people who would oppose them.
So what’s going on behind the curtain?
One very real possibly is a direct, planned attack on the world economy by a number of players: China, Russia and their allies.
The reasons for this take some research, but look at how China arrested a whistle-blower in December for attempting to warn the press about the existence and spread of the COVID-19 virus. Also look at how long China did not report it to other countries. They still may not be reporting all the numbers. But more importantly, look at how quickly the Chinese infection rate turned around compared to other countries.
China has huge tension with the United States because of the trade war, and the United States stands in the way of China’s goal of being the next world superpower. And what better time to launch an economic attack than during the year of a Presidential election in the United States.
Creating panic is critical to causing the fear, worry, doubt and panic necessary to disrupt the normal flow of money and productivity in our already very fragile economy. The West is an open society, and with the free flow of information and disinformation through news and social media… creating confusion and panic is all too easy.
Also, if you missed it, Chinese investment firms swarmed the United States stock market when it took its dive, and bought a very large number of US Corporate stocks. They’ve gained a larger influence and income stake (not just ownership) in our assets.
Several attempts have been made, and they won’t be the last, to attach bills to the economic relief packages which would not otherwise survive proper review.
Back in 2001, there was a bill which had been drafted months before the terror attacks of September 11th. After the attacks, the bill was quickly formalized and named “The Patriot Act”, and was passed because of the panic and fear created by those attacks. After all, who could stand out in public and decry a bill which overrode most Constitutional protections (allowing courts to be bypassed in the name of national security) when it had such a hallowed title of “Patriot” in its name, and Patriotism was enjoying a great resurgence. Without the attacks, that bill would have had no chance of passing. And with the passing of time, newer generations are only aware of it and not the damage it did to us as a country. In my opinion, the bill did far more long-term damage than the attacks themselves.
So what is being passed now. Well, the answer is to watch any bill being passed with “economic relief” in the title. Attempts so far:
- There was a recent Supreme Court decision which ruled against public funding of abortions, and the decision stopped millions of taxpayer dollars per year from going to Planned Parenthood. An addition to the Corona Virus economic relief act was attempted by several members of Congress (Senator Nancy Pelosi was among them). It was removed after a public outcry.
- In addition, many items for funding the Green New Deal were also thwarted. These items sought to channel a significant portion of the money into a project called the “… New Deal” which borrowed the term from President Franklin D. Roosevelt’s project to steer the economy out of the depression. Remember what I said about using the term “Patriot”?
- Many local governments are struggling to keep their executive orders at the level of “strongly recommended” without going to “mandatory”. One of the biggest dangers of this virus isn’t the outbreak, but people trying to use people’s reactions as leverage to toughen the laws. Some places, Vermont in particular, went to marshal law. I completely disagree with their action: it was unwarranted, and should serve as a major warning of the true danger of letting ourselves be worked into a frenzy over this outbreak.
The strongest indication of how healthy a republic is, can be seen by the will and ability of its free people to self-govern. President John F Kennedy phrased this as “ask not what your country can do for you, but what you can do for your country.”
I want to leave you with a perspective on this. In the early 1980s, the U.S. Federal Aviation Administration addressed the issue of ultralight aircraft (hang gliders, etc) due to a few reports of some near misses with private and commercial aircraft. The ultralight industry was gaining in popularity.
After numerous meetings and public comments, the FAA released Part 103 of its regulations for these aircraft. It is an interesting regulation for two reasons.
First, there are numerous statements about understanding the needs of certain things (like pilot licensing, maintenance, aircraft certification. etc). Almost all of them basically end with the statement that the agency does not see the reason to regulate this at this time. The document is labeled as a regulation, but it actually only regulates the size of the aircraft and its use. It’s rare to see a regulation which contains so many things which are only suggestions.
Second, an interesting statement came from the FAA administrator at the time they released the regulation. He stated the purpose of the regulation was actually “don’t get our attention.” His statement truly reflects that content. He was warning that while the FAA was trying to let the ultralight community self-regulate, any pattern of failing to self-regulate would require them to come back–and regulate.
Has it worked? There has been no change to those rules in 37 years since they were released in July of 1982.
Keep this in mind as you navigate this pandemic. There are plenty of people at the top (or who like to think they are at the top) who will have an answer. The more we can respond with “Thanks, but no thanks”, the more this situation will have a good ending.
02 Apr 2020
COVID-19: An simple exercise in evaluating information
I recently read this article discussing a possible cover-up in the number of deaths from COVID-19 in the town where it originated: the city of Wuhan in China, population around 11 million people. This is a great article to expand upon, in doing some basic sanity checks to check the numbers. There is another article from the NY Post which repeats some of the information in the first article here.
Warning: the thought of people’s loved ones being turned into a numerical body count is not pleasant, nor is it my intention to desensitize anyone to the value of life. I have spent quite a bit of time keeping all of this in prayer, after all Jesus is the great comforter, nonetheless there has to be an unemotional evaluation of information. And that is what I am doing here.
The article uses the following information to claim that the death toll is much higher than expected. These are the facts stated in the article.
- A Radio Free Asia analysis, for example, found Wuhan’s official death toll of 2,535 may be understated by a factor of 20.
- It reported seven mortuaries were handing families 500 funeral urns a day for well over a week.
- One took shipment of 5,000 urns in just two days.
- People in Wuhan have reported that the crematoriums have been running non-stop day and night.
If #1 is correct, the assumption is that the number of deaths could actually be 20 x 2,535 or around 50,000+. The article from business insider claims the factor is between 5 and 20, so the low end would be 12,500+.
Number 2 is either 7 x 500 urns (3,500) during a week if the seven mortuaries comprise the total number to together, or 7 x 7 x 500 (25,400) if each of the seven mortuaries handled 500. The context is not clear on this one.
Number 3 implies that a single mortuary took a shipment of 5,000 urns in a two-day period. If all 7 are doing this, that’s 35,000 urns in two days among those seven mortuaries.
Number 4 is hard to qualify with numbers and is more hearsay, and for this exercise can be disregarded.
So how does this compare to a time when COVID-19 is not spreading?
Sometimes, the sheer volume of everyday things in the world eludes us. The cycle of life is one of them. We hear about the numbers of people dying from the virus, but what’s a typical count of people dying on any given day look like. That’s important to know, to keep perspective. And here is an easy way to calculate it:
- Go to Google and enter “world population now”. The result is 7.53 billion.
- Go to Google and enter “average lifespan worldwide”. The result is 72.6 years.
- If you take population and divide it by lifespan, you will come up with the average number of people born per year: 7,530,000,000 / 72.6 = 103,719,008 which is also the average number of people who die per year (although it will be lower than the birth rate, since population is growing).
- If you take the number of people born in a year and divide it by 365.25 (365 days per year, and include the extra day per leap year), 103,719,008 / 365.25 = 283,967
So on any given day in the world, 283,967 people are born, and roughly the same number come to the end of their life. Now a note about this number: 72.6 years is a median average. There are a number of people who die at younger ages, but the average is what we will use for this example.
So the epicenter for the COVID-19 breakout is Wuhan China, a city of 11.08 million people (Google result again). To calculate the average deaths per day in Wuhan, we first calculate the percentage of the world’s population which lives in Wuhan (11,080,000 / 7,530,000,000) or 0.0014714475431607 (0.14714475431607%). Now multiply this by the average number of deaths per day in the world calculated above (283,967), and on any given day there should be roughly 418 people in Wuhan who die. And this number is outside of any COVID-19 presence.
So does this make sense? And how do the numbers being talked about compare with this.
It’s hard to tell. Looking at number 3, a shipment of 5,000 urns in a two-day period could just be a regular restocking event. Assuming (and yes it is an assumption) that Wuhan has seven mortuaries, there would be 60 bodies delivered to each mortuary per day. 5,000 urns at a single mortuary would last 83 days, assuming all 60 per day were cremated and needed an urn. The arrival of urns themselves doesn’t indicate a rise in deaths, although a 60+ day stock on hand would seem higher than normal.
There are also other pieces of information which are missing and needed to do an accurate assessment:
- An accurate reporting of deaths, which does not seem to be forthcoming.
- Is the number of mortuaries in Wuhan actually seven, or are only seven of a higher number being discussed.
Just using the 418 deaths per day says that 2,226 people die per week, and 12,540 die in a 30-day month. So the numbers of urns being handed to families and the numbers of urns arriving, by themselves, are not out alignment with regular usage.
Conclusion
As much as I hate to say it, there are a lot of people who are saying that the impact of this disease is being hyped above what it is actually doing. This type of article and its content actually argues for their point. Why?
- Accurate numbers of deaths would clearly show whether the disease is as dangerous as being reported, or not.
The article reports what people are reporting they have seen (second hand information), but makes no mention of whether any question was asked directly to the mortuaries themselves to see if they could provide any of:
-
- What is the normal daily use of urns, compared to the number used during the pandemic?
- What is the number of bodies your facility has processed in the pandemic, versus the same time last year?
- Whether the answers would even be given, or whether the information would be refused.
- Hearsay and unverifiable information only adds to speculation, and that gap of information only breeds fear and paranoia.
As much as I could borrow the Mythbusters rating system, I really can’t in this scenario. There are just too many information gaps. But looking at the scale of life and death I have shown, your challenge is now:
- To evaluate the number of people succumbing to the effects of this disease, while
- Keeping the value you put on life intact, and ever wondering
- How big is our God, when he states that he knows his own people, and not one will slip from his grip unnoticed.
30 Jul 2019
Think Twice Before Escalating Anything
A few weeks ago, I read the new reports based on tweets made during the diversion of a flight, on which Keanu Reeves was travelling. And it left me a little disturbed about our social media focused society.
The plane had a minor mechanical issue and had to divert to Victorville, CA, instead of continuing to its intended destination. It was uneventful, and Keanu Reeves was photographed in a number of selfies and praised by everyone for the way he acted in response to the incident with his interaction and kindness. That’s admirable. But what was very disturbing was the reference by numerous people on the plane to Keanu Reeves as a “hero” on their tweets.
Hero?!
Isn’t that the term we use for the police and fire personnel who risk the lives for life and justice? Isn’t that the term we use for valor in military action that fights evil and saves lives? And more importantly, is that the only word that comes to people’s minds when they wish to praise someone publicly? Seemingly, this is the way things are sadly headed… especially in social media.
To be clear, Keanu Reeves actions were indeed praiseworthy, but poorly mislabeled. He did what would make a father or mother proud of their son. He was the model of a gentleman. If you’ve never seen the movie, I recommend you watch Blast From the Past (1998, Brendon Fraser). Dave Foley’s character reads the definition of a gentleman he looks up in the dictionary: a man who goes out of his way to make sure that the people he is with feel comfortable around him. Other than using the word woman, the definition is no different for a gentlewoman. You won’t find the definition written like that in Google: it’s answer is in the context of a title, and is far too shallow.
This is a very ugly effect of the super-hero culture we live in today. Since social media requires people to speak up to be heard (and usually loudly or using shock tactics), the superhero character appeals to the masses because 1) superheros do great and inspiring things, and 2) superheros get mass recognition. But to label what Keanu Reeves did as “superhero” shows how this escalation has gotten out of control. The Romans documented hundreds of years ago something called the seven traps in logical arguments. They basically list seven traps which begin with “argument based on …” with names like “unverifiable authority”, “emotion”, etc. Labeling an act of kindness as if it is an act of heroism is “argument based on emotion”, and in this case… destructive hyperbole.
It is important to realize that escalating anything beyond what it requires, raises (or lowers) a standard which should not have changed. If you feel the need to post something on Facebook, leave out the temptation to give it an emotional sales pitch. Let the event or article speak for itself.
It is, in fact, a form of crying wolf… which can done with both complaining and praise.
16 Mar 2019
Unexpectedly Joining the Distributed Workforce
After an unusual set of circumstances, my company has shifted its IT and software development staff into a distributed workforce even though all of us are within a local drive of the office. Previously other terms were used for this type of work, like working from home or working remotely. But it is so much more than that.
The distributed workforce is becoming a common buzzword now, describing people who rarely or never come to a physical office. It’s a new world for me, but not for my wife. She worked for a company in Pittsburgh for a year, before we decided to move back to Florida. She had proved herself to be quite an asset, and the company allowed her to take the company laptop and other equipment with her and give it a try. It has worked quite well for her.
Matt Mullenweg, the co-creator of WordPress blogging/content management software, has produced a video on the distributed workforce here. His new company is 100% distributed workforce. Ironically, my wife has been working for over 18 months in Florida and there were 14 people in the office when she left Pittsburgh for Florida. There is now only one person in Pittsburgh who goes into the office, so the idea has even caught on with her company.
So after about two months in the distributed workforce, here’s what I have found:
The Good
You get a certain part of your life back by losing the commute to the workplace. Another part of this is lowering the stress from rush hours, overly assertive drivers (aggressive is a label), accident delays and other negatives to a regular commute. There is also a savings in fuel costs, toll road costs, and maintenance (less wear and tear), although those costs won’t totally go away.
You can choose where you work, at pretty much anytime. The terms “working from home” and “working remotely” are too narrow, so the distributed workplace implies any place other than a fixed location:
- You can decide to spend sometime in another location and just work from there. My wife and I recently went to Kansas City, where our daughter goes to school, to have some time with her and take care of some chores at the house. Some of my coworkers have or will shortly be working from out of country–just to have a change of pace. I often see distributed workers just hanging out for an hour or two at a Starbucks or other place with free WiFi.
- A group of your co-workers can decide to work in a public area for several hours to collaborate in person. I recently did this with some coworkers to coordinate the final stages of a project for deployment. It was a newer marketplace with a microbrewery and food shops, and we went in the middle of the week when the volume of shoppers was low. The merchants were happy to see us and others with laptops showed up in the marketplace. This gave me a fresh perspective on the value of the buy local movement.
- Your home office is your own environment, which gives you a lot of control. Being a software developer, immersion is a key aspect of developing code. I worked for 8 years in a Microsoft-like environment, which was private offices with a door. Closing the door was only done to block out the rest of the office for some immersion time. This gets really good in a home office, because people can’t just walk up to you and disrupt you when you are immersing. Also, in areas where there is no office, it is amusing to see the 50/50 split among the workers who want overhead lights on or off while working at their workstations. The home office eliminates that debate.
The Bad
Initializing social contact becomes a proactive effort. In the office environment, people often initiate conversations by simply coming into contact with another by chance. Because the distributed environment eliminates this chance contact, there has to be some initiative to create some chance contact. At a minimum, companies generally plan some kind of team activity when everyone can relax together. This is a good reason to set up a permanent video conference called “the water cooler” so that people can just check-in outside of scheduled meetings, say hi and chat with whoever is there.
It requires diligence to keep up with all the things happening on the team, and to report all the things through more formal channels in the team. Similar to chance conversations, being distributed also eliminates hearing about something from another conversation nearby which should have been communicated. The “water cooler” open video conference can sometimes help with this, and can be a good measure of where documentation or communication is lacking.
It requires a high level of self-discipline. While I list this under the bad part, it is only the adjusting or re-adjusting to the lack of immediate personal feedback. It is not too difficult if you’ve worked independently before, but leaving the office environment where your team is physically present will require this shift.
If you are not in the habit of exercising, get started as soon as possible. For some people who are not involved in regular exercising, working in the distributed workforce can actually remove the only form of exercise they have: walking to the office. Where we live, we have a community pool and a nice 1.5 mile walk we can take daily. Find whatever works for you and do it. It helps to avoid feeling isolated when you are not often around your work team, and the exercise is always good for your health.
The Good or The Bad … Depending upon your situation
The home life can not interfere with the office time. My wife and I are now empty-nesters in middle-age, so this is not a problem for us. She has her office in the front of the house, I have mine in the back. The only time we see each other when we are working is when we take a cappuccino break, or sometimes even lunch. If my kids were still living at home (especially under the age of 5 or 6), this could be a challenge to manage. Still, I’ve seen some people manage it amazingly well.
Some final thoughts on why this is growing into the norm for a lot of companies
The idea of work following the sun (as Electronic Data Systems used to refer to work transferring from one team to a team on the next continent on a near constant basis) has been around in some valid form since the 1990’s. Remote working is not new. But there have been several events in technology and culture which have made wide adoption of this work phenomena possible:
The switch to SaaS (Software as a Service) and the extensive adoption of the cloud.
As a software developer, it was difficult to envision, even just 5 to 10 years ago, being able to write code and manage build processes while outside of a secure office environment. The build servers were generally in some restricted part of the company, and the development and testing process stayed on corporate owned and managed servers–often in the corporate facility itself. The production servers, where the product was deployed and served the public, was the first place the code was operated outside of the corporate IT department. Usually, this was on hosted servers in one or more data centers.
With the advent of the cloud, and Software as a Service impacting even the coding and build tools (Azure, Amazon S3, GitHub), source code and build processes now exist outside the company’s IT department hardware. The IT and DevOps folks are just tenants of a larger system in the cloud. In fact, in my current position, I don’t use a VPN except on rare occasions to directly access a server on Azure or a corporate server with legacy info which has not yet been transferred to a SaaS service.
So while distributed work was enabled by the tools software developers built, now even the development process itself is distributed work.
The incredible growth of high speed internet between continents
Back when the United States began military action in Afghanistan after the September 2001 attacks, I remember the almost comical transmission delays when a news agency (CNN, etc) did a live report from the scene. Since the primary signal transmission went over a few satellites to transit over the continents, the delay was often 2-3 seconds. Most inter-continental internet traffic still traveled over satellites at the time as well. The delays were annoying, but I do remember it being fodder for a Saturday Night Live skit about two comics separated in Afghanistan and the United States were trying to do their routine over the “live” link. It was more irony for me, in that the same timing disruptions they experienced in trying to do their routine in the skit, was something I was experiencing when talking to overseas teams in India at the time.
A signal travelling to a (geosynchronous) satellite has to travel 22,236 miles, and the round trip is 44,472 miles. When you consider that the speed of electricity is 182,000 miles/sec, that’s almost a quarter of a second travel time. If it has to travel over multiple satellites, it’s roughly 1/4 of a second per satellite. And in a phone call or video call, that’s just the delay from the microphone on the far end to the speaker on your end. That same delay occurs when you answer back.
About four months ago, the company I now work for contracted with a company in India to do some coding. And as we did work with them over video links using Zoom, it was immediately clear that something had radically changed. The timing delays were gone… all of them. I was so pleased with how much the absence of timing delays made the conversations more natural.
Curious to what had caused this, I did some quick research. The reason it has improved so much is that today 97% of all intercontinental internet traffic is carried by an undersea fiber optic cable. 97 percent ! How far we have come in just over a decade. Undersea cables (copper) have been around for many decades, and were designed for telegraph and telephonic transmission across continents. There has been a substantial amount of effort to lay undersea fiber optic cable to increase the speed and capacity between land masses.
When the undersea fiber optic cable is used, the travel distance from Florida to India is about 10,000 miles. In addition, when the signal changes cables during its route, it does so at a junction box right in the cable. This increases the travel distance only by yards or feet–not by multiples of the entire distance. This cuts the one-way time for the signal to travel down to between 5/100ths to 10/100ths of a second, making the response time difference very noticeable.
To get an idea of the extent of underwater intercontinental fiber-optic connections, check out this map. The cables represented by a grey color are not yet operational and have the planned date of launch next to their name.
In conclusion
The distributed workforce is one of the gems of the global village envisioned long ago, and should be embraced. It opens up a world of possibilities. And I really like it.
A side note: My wife and I worked (not distributed) for the same company from 2007-2015. We are now both distributed workers working from home, but for different companies. We’ve kinda come full-circle.





